Tips and Advice to Avoid Common Scams in 2023
Over 3.4 million scam phishing emails are sent daily, becoming increasingly complex and sophisticated. Because of this, protecting your accounts is getting harder and harder. Depending on the structure of the scam and the hacked account, regaining access can be a long, frustrating, and sometimes fruitless process. That is why we recommend making prevention a critical component of cybersecurity for businesses of any size.
To help, we’ve provided some of our top tips that you can implement today to protect yourself and your business.
Be Alert
We recommend protecting your accounts from hackers by not engaging with them in the first place. Avoid online/phishing attacks by being aware of scam email alerts. They mimic platform alerts, messages from friends, or even emails from your boss.
Confirm emails you are in doubt about. And don’t click on any links, open any attachments or give over any information if you’re not sure it’s authentic. You can also search for information about the suspected scam online to see if others have received similar emails/calls.
Verify & Confirm
Common scams we see involve people receiving “support” messages/platform alerts or messages from friends, colleagues, managers etc. Knowing how to verify and confirm a message is safe can help you protect yourself and your accounts. We’ve included examples of common scams below.
Platform/Tech Support Alerts
One of the most common scams we see are emails designed to look like platform alerts. Like Meta telling you that your account has been flagged for violating a policy, or requests to update your information. There are a myriad of other things from many different platforms. These emails then ask you to follow a link to resolve the issue. After opening the link you are asked to enter your login details into a platform that looks exactly like you would expect it to (they even spoof the URL). Once this is done they will use that login information to gain access to your real account and kick you out.
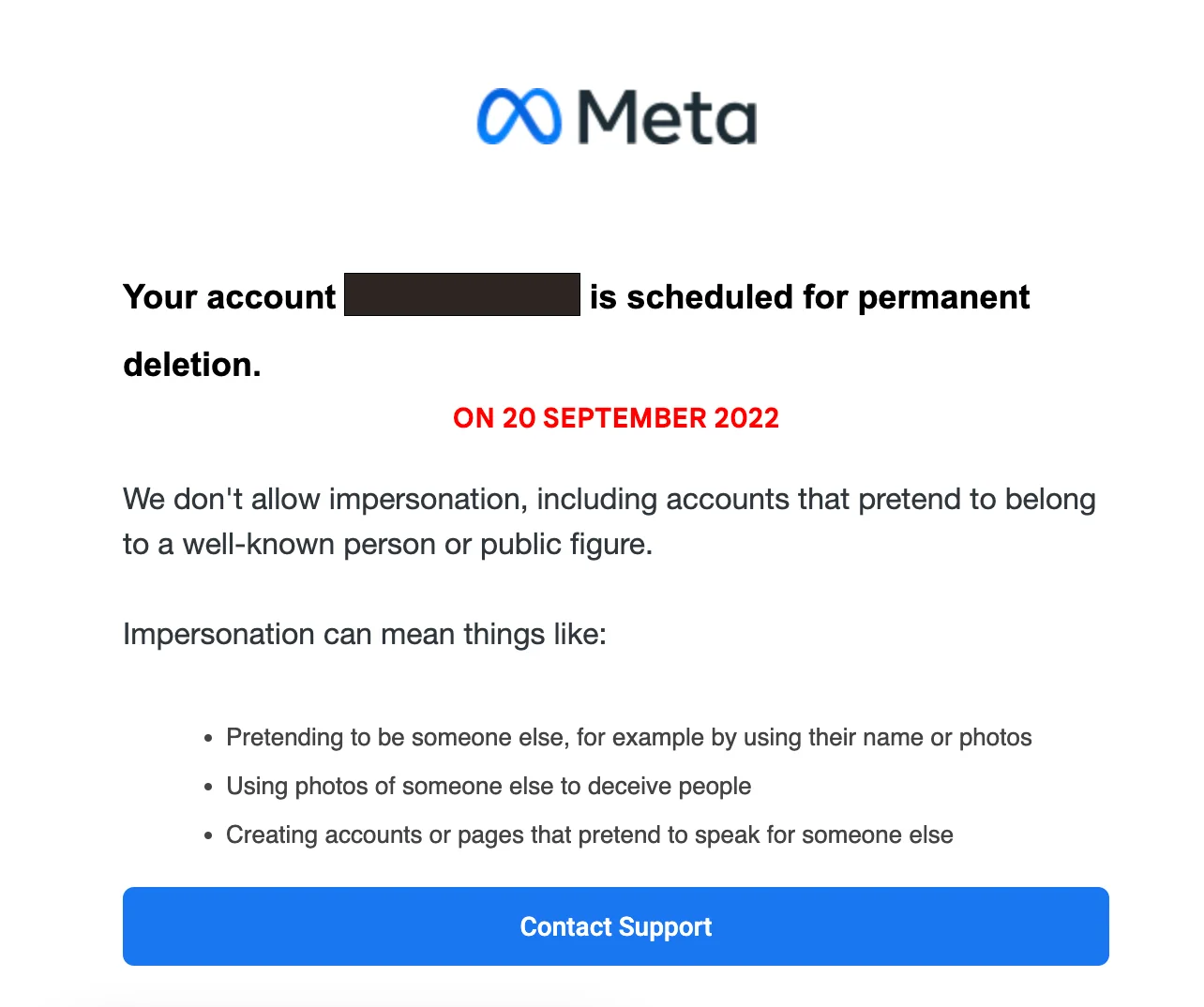
To avoid this kind of scam you can follow the steps below:
- Carefully inspect the email address. Look for clues that might be an immediate giveaway that this is not a real platform email.
- Log in to the platform in question directly (not via the link in the email). Look for an alert that mirrors what you are seeing in the email. Most platforms will show a pop-up or banner for anything important for you to know.
- If you are still wary, we strongly suggest screenshotting the message and having someone you trust or your digital agency give their opinion.
- Remember the messages are designed to make you panic! It’s always better to take your time and do your due diligence than open yourself up to a potential scam.
Messages From Friends
Hackers can also gain access to one social media account. Then they use that account to gain access to others by pretending to be the original user. This will usually come in the form of a message from someone asking you to help them in some way. One of the most common ones we see is a friend letting you know they will send a code to your number for you to give back to them. The hacker then sends you your own 2-factor code to gain access.
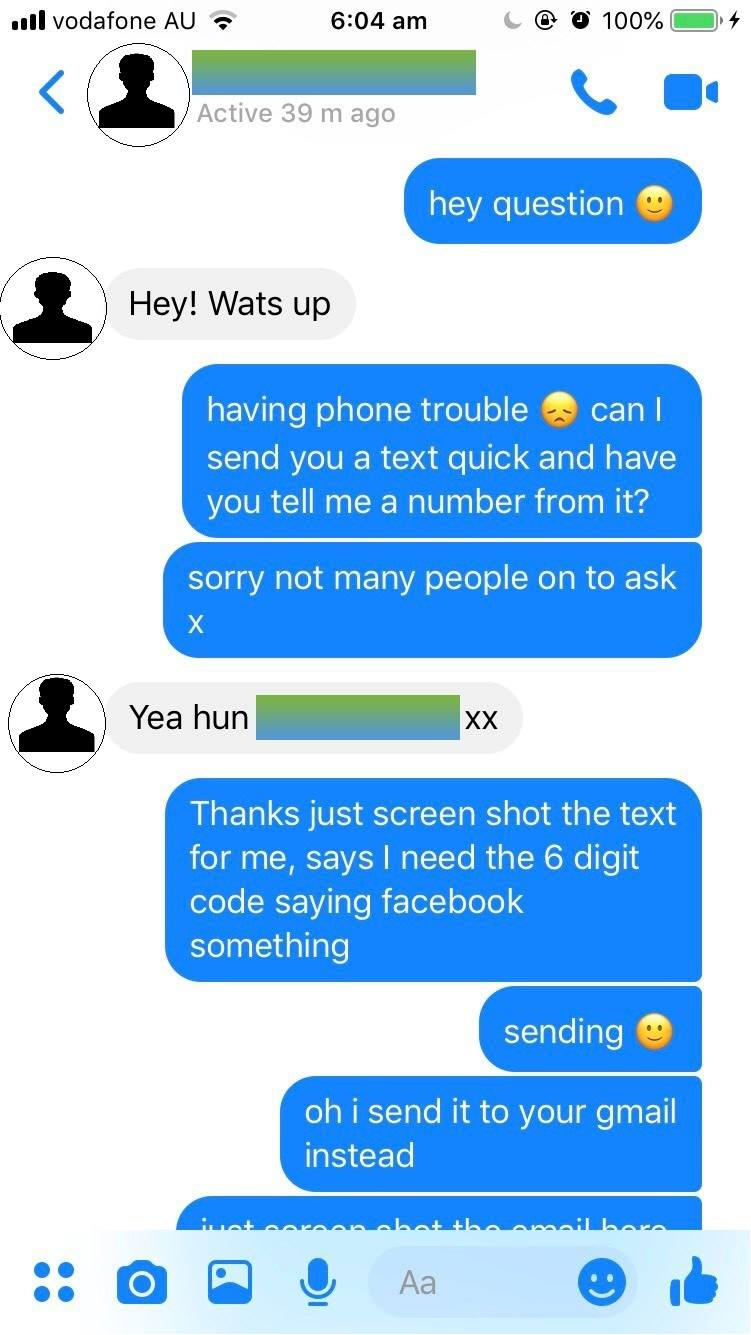
To avoid this kind of hack you can follow the steps below:
- Consider whether this makes sense – would this person reach out to you this way? Does it sound like them? These can be the first indications that something is wrong.
- Verify their request through a different platform. Ideally, we recommend giving your friend a quick call and checking if it really is them, but contacting them through any platform other than the one you are on will do the job.
- Until you are able to verify the request with your friend do not click on any links or reply to the message. Better safe than sorry!
Email Spoofing
Email spoofing scams work by using a technique to make the email appear as if it is coming from a legitimate source. This could be your boss, a coworker, a client or anyone else the scammer knows you are likely to trust. These emails will usually ask you to click on a link or open a file for any number of reasons.
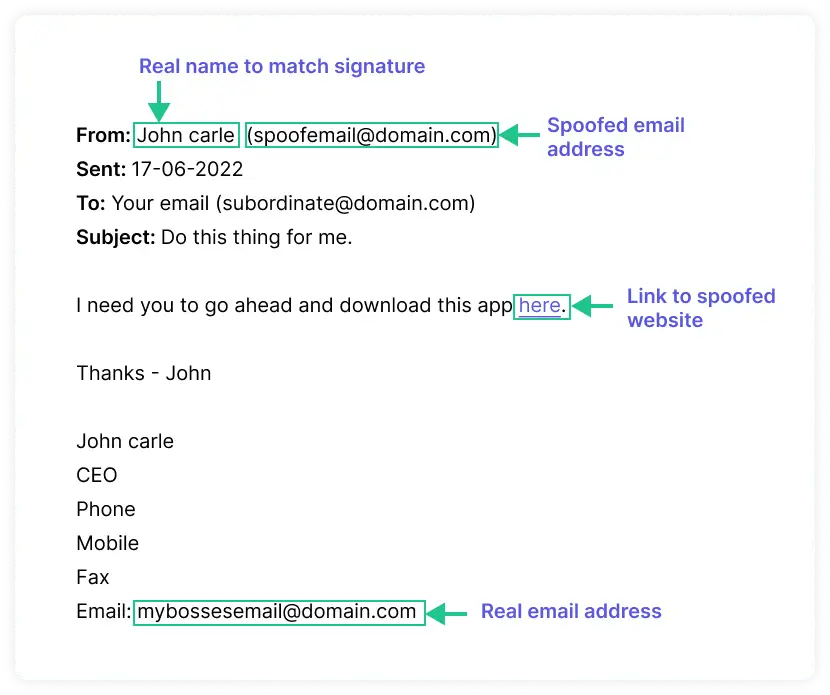
This kind of hack can be tricky to avoid particularly in a work environment because we can sometimes go into autopilot when sorting through our inbox. To avoid this you can follow the steps below:
- The most impactful thing you can do is to consider whether this email is something you would expect to receive. If it seems out of place or you weren’t aware it was something they wanted done then take a second to verify the request.
- Verify, verify, verify. Ask your colleagues if they received the same thing and check with the sender to confirm their request.
- Be cautious of texts as well – while email phishing scams are by far the most common it is also possible for hackers to spoof phone numbers, so be sure to apply the approach above to texts and phone calls as well!
Two-Factor Authentication
We know, we know, this is the advice that every single platform, blog and man on the street is giving you BUT it is definitely one of the most critical steps to protecting your accounts. With that being said 2-factor can produce its own problems if you lose access and lock yourself out of your account, so when adding 2-factor, here are a few extra steps you can take to make sure you don’t lock yourself out:
Multiple Methods:
When possible try to use various methods of 2-factor so that you have options should something happen. Options usually include:
- Authenticator App (if you don’t know what this is – ask one of our team to help you set it up)
- Mobile Phone
Using a variety of methods means that if one goes down, e.g. if you lose access to your email then you will still be able to access your account by other means.
Backup Codes
Most platforms give you the option to add backup codes. These are a set of codes that can be printed out and used should you lose access to all other means of 2-factor authentication. Print these codes out, or write them down and then store them somewhere safe. This effectively gives you a master code to access your account should you get locked out. Facebook’s guide to adding backup codes can be found here. Google’s guide for adding backup codes can be found here.
–
We know that it can feel overwhelming sometimes to take on hackers and protect ourselves and our businesses, but by implementing the practices above into our digital lives we can stop them in their tracks. Remember that practice makes perfect and if you keep these tips top of mind they will soon become second nature.
If you’re uncertain about where to start, want clarification on any of the recommendations in this guide, or you’re ready to chat about your digital presence please reach out to our team, we’re here to help.


